In today’s digital age, securing access to sensitive systems, data, and applications is more critical than ever. With rising cybersecurity threats and remote work environments, businesses must ensure only the right people can access the right resources. This is where access management plays a vital role. But what is access management, and why is it so important for organizations today?
In this comprehensive guide, we will explore what is access management, how it works, the difference between access management and identity management, and the leading access management solutions shaping the future. Whether you're an IT professional or a business leader, this guide offers a simple and complete understanding of access control and identity solutions.
Table of Contents
- What is Access Management?
- How Access Management Works
- Access Management vs. Identity Management
- Access Management Solutions
- Why Access Management Is Important
- Key Features of Good Access Management Systems
- Future of Access Management
- Conclusion
What is Access Management?
Access management is the process of controlling who can access specific digital resources and under what conditions. In simple terms, it answers the question: "Who is allowed to access what, and when?"
What is access management really about? It ensures that only authorized users can log in, interact with, and modify digital resources within an organization. Access management works in harmony with identity systems to validate users and assign permissions based on roles or policies.
If we define access control, it is a broader concept that includes both identity management and access control, where identity determines who a user is, and access control decides what they are allowed to do.
By implementing effective access management solutions, organizations reduce the risk of data breaches, unauthorized access, and compliance violations.
How Access Management Works
Understanding how access management functions will help you appreciate its value. Here's a step-by-step overview:
1. User Identification:
The system identifies users through credentials such as usernames, passwords, biometrics, or tokens.
2. Authentication:
Verifies if the user is who they claim to be. This often involves multifactor authentication (MFA).
3. Authorization:
After authentication, access management evaluates user roles and permissions to determine what resources they can access.
4. Access Enforcement:
The system enforces the rules and either allows or denies access.
5. Audit and Monitoring:
Logs every access attempt to help with tracking, compliance, and security analysis.
For instance, access management login portals allow users to enter credentials, verify identity, and get access to their respective dashboards or systems.
Access Management vs. Identity Management
Although often used together, access management and identity management serve different functions in the digital ecosystem.
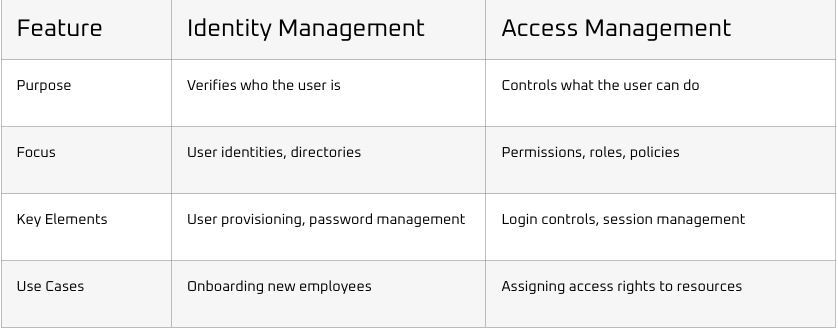
In summary, identity management and access control work hand-in-hand. First, we identify the user, and then we apply the necessary access controls to ensure secure and appropriate access.
Access Management Solutions
There are several robust access management solutions available today that help secure organizations. These tools ensure smooth authentication, authorization, and compliance.
Some leading access management platforms include:
1. Trevonix:
Trevonix is a global leader in Identity and Access Management (IAM) services. Trevonix provides advanced, scalable IAM solutions tailored to enterprise needs. They specialize in secure login, role-based access control, and IAM automation.
These access management solutions support access management login, risk-based authentication, and centralized user role enforcement.
Why Access Management Is Important

Still wondering what is access management good for? Here are key reasons why organizations must prioritize it:
- Security: Prevents unauthorized access to systems, reducing risk of data theft.
- Compliance: Meets industry standards like GDPR, HIPAA, and ISO.
- Productivity: Enables employees to securely access what they need without delays.
- Centralized Control: Manages user permissions and access across the entire IT environment.
- User Experience: Supports seamless, secure access management login for employees and partners.
Without a strong access management framework, businesses expose themselves to insider threats and regulatory penalties.
Key Features of Good Access Management Systems
A powerful access management system should have the following features:
- Single Sign-On (SSO): One login for all systems.
- Multifactor Authentication (MFA): Extra layers of security beyond passwords.
- Role-Based Access Control (RBAC): Assigns access rights based on roles.
- User Provisioning and Deprovisioning: Quick onboarding and offboarding.
- Audit and Compliance Tools: Tracks user activities and access logs.
- Integration Capabilities: Works with existing infrastructure.
- Self-Service Access Requests: Users can request access with automated approvals.
Trevonix offers many of these capabilities within their IAM services, making it a preferred partner for secure digital transformation.
Future of Access Management
As digital transformation accelerates, access management is evolving. Here's what to expect:
- AI-Driven Access: Using machine learning to detect and respond to unusual behavior.
- Zero Trust Architecture: Verifying every user and device before granting access.
- Passwordless Authentication: Biometrics, mobile tokens, and hardware keys will replace passwords.
- Cloud-Native IAM: Solutions designed specifically for hybrid and multicloud environments.
- Decentralized Identity: Giving users control over their own digital identities.
Organizations like Trevonix are at the forefront of adopting these trends to provide future-ready access management solutions.
Conclusion
So, what is access management? It's the backbone of secure digital operations. From access management login portals to full-blown identity frameworks, businesses today need robust controls to protect sensitive assets.
By implementing the right access management solutions like those offered by Trevonix, you can:
- Define who gets access
- Control how and when they get it
- Monitor and secure the entire access lifecycle
Ultimately, effective access management is not just a security measure—it’s a strategic business enabler. Make it a priority today.






