In today’s digital-first world, almost everyone depends on email, online banking, social media, and cloud applications. But with these conveniences comes a growing threat: phishing attacks. If you’ve ever received a suspicious email urging you to click a link, download an attachment, or urgently update your account, you’ve likely encountered phishing.
In this blog, we’ll provide a clear phishing definition, explain what is meant by phishing attack, explore its impact in cybersecurity, review the different types of phishing scams, show how phishing attack works, and provide practical steps to protect yourself and your business.
Whether you’re an individual, a small business owner, or part of a global enterprise, understanding phishing is crucial to protecting your data, money, and identity.
Table of Contents
- What Is the Definition of Phishing?
- What Is Meant by Phishing Attack?
- Phishing Definition in Cyber Security
- Types of Phishing Scams
- How Phishing Attack Works
- Real-World Examples of Cyber Phishing
- How to Prevent Phishing Attacks
- Conclusion
What Is the Definition of Phishing?
The phishing definition is simple: phishing is a fraudulent attempt to trick individuals into sharing sensitive information such as usernames, passwords, credit card details, or bank account numbers.
In phishing, attackers pretend to be trustworthy entities—like your bank, a government agency, or even a coworker—while sending fake emails, text messages, or creating lookalike websites. Their goal is to deceive you into giving up confidential data.
To put it plainly: phishing is like a con artist showing up at your door pretending to be from the electric company so that you’ll hand over your personal details. Online, however, the scam happens through emails, SMS, websites, and sometimes even phone calls.
What Is Meant by Phishing Attack?
Now that we’ve seen the phishing definition, let’s expand on what is meant by phishing attack.
A phishing attack means a deliberate attempt by cybercriminals to obtain sensitive information from a victim by impersonating a legitimate source. These attacks often look harmless at first but are carefully designed to trick you into clicking a link, downloading malware, or typing confidential information into a fake site.
Real-Life Phishing Examples:
Email Example:
An email claiming to be from PayPal, warning that your account will be suspended unless you “verify your identity.” The email contains a fake link leading to a counterfeit PayPal login page.
Fake Website Example:
A website that looks identical to your bank’s portal but is actually a clone created by hackers. Any credentials entered go straight to the attacker.
SMS Example:
A text saying “Your package is waiting. Click here to confirm delivery” with a malicious link.
The phishing attack meaning is all about manipulation—attackers rely not on technical hacking skills but on exploiting human trust.
Phishing Definition in Cyber Security
When it comes to phishing definition in cyber security, it refers to one of the most common and dangerous social engineering attacks. In cybersecurity terms, phishing is classified as a technique where attackers deceive users into compromising their personal or organizational security.
Phishing is at the root of many data breaches, ransomware infections, and identity theft incidents. According to global studies, over 80% of security breaches begin with a phishing attempt.
Why Phishing Matters in Cybersecurity:
- For Businesses: Phishing can compromise financial accounts, trade secrets, and customer databases.
- For Banks and Financial Institutions: Attackers often mimic banking portals to steal customer login details.
- For Individuals: Victims may lose money, suffer identity theft, or unknowingly install malware.
In short, the phishing definition in cyber security highlights the importance of awareness. It’s not just about technology—it’s about people being aware of how attackers manipulate trust.
Types of Phishing Scams
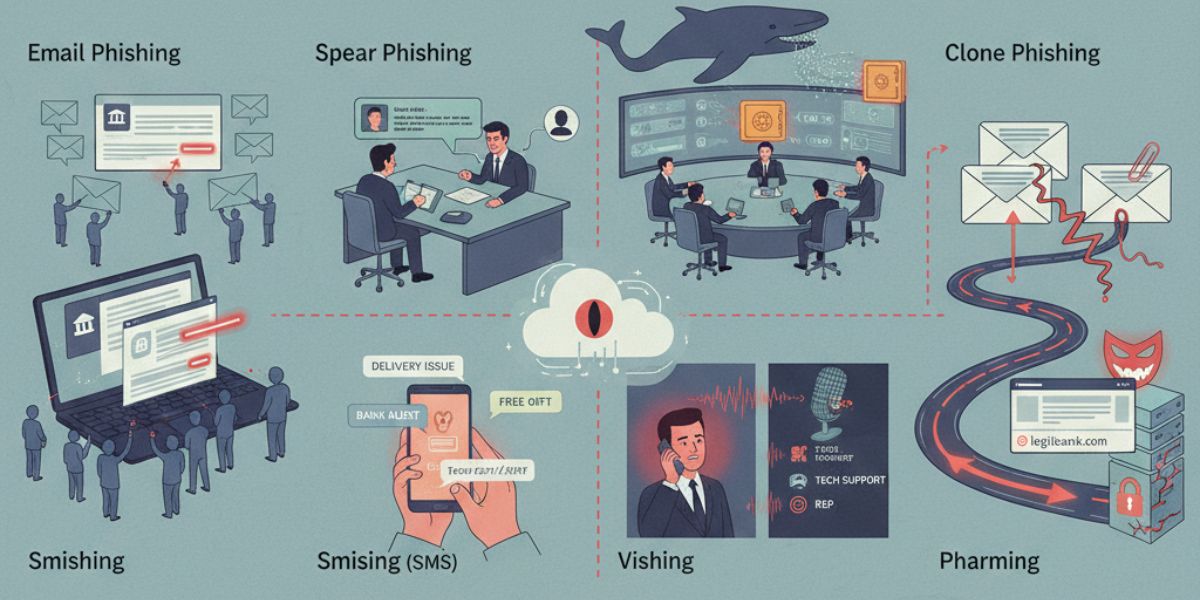
To fully define phishing scams, we need to look at their different forms. Attackers constantly evolve their methods, making phishing one of the most versatile cyber threats.
1. Email Phishing
The most common type, where attackers send fraudulent emails that mimic legitimate organizations.
2. Spear Phishing
Highly targeted phishing emails sent to specific individuals, often using personal details to appear genuine.
3. Whaling
Aimed at high-level executives like CEOs or CFOs, trying to gain access to corporate financial accounts.
4. Smishing (SMS Phishing)
Phishing via text messages, often claiming delivery issues, bank alerts, or fake promotions.
5. Vishing (Voice Phishing)
Attackers make phone calls pretending to be technical support, IRS agents, or bank representatives.
6. Clone Phishing
A legitimate email is duplicated but with a malicious link or attachment added.
7. Pharming
Attackers redirect users to fake websites even when the correct URL is typed, often through DNS poisoning.
By clearly defining phishing scams, we can see how wide-ranging and creative cybercriminals can be.
How Phishing Attack Works
Understanding how phishing attack works helps in detecting it before falling victim.
The Step-by-Step Process of Phishing:
- Planning – The attacker selects a target and gathers information.
- Bait Creation – A fake website, email, or SMS is crafted to look authentic.
- Delivery – The phishing message is sent via email, text, or call.
- Hooking the Victim – The victim clicks a link, downloads malware, or provides credentials.
- Exploitation – Stolen information is used for fraud, identity theft, or unauthorized access.
The scary part? Phishing often succeeds because attackers use urgency and fear tactics like:
- “Your account will be closed if you don’t act now!”
- “Suspicious login attempt detected. Reset your password immediately.”
This psychological manipulation is why so many people fall for phishing scams.
Real-World Examples of Cyber Phishing
To truly understand cyber phishing, let’s look at real-world incidents:
- Google and Facebook Scam (2013–2015): A hacker tricked both companies into wiring him over $100 million by sending fake invoices pretending to be a legitimate vendor.
- Target Data Breach (2013): Attackers used phishing emails to access vendor credentials, leading to one of the largest retail breaches in history.
- COVID-19 Phishing Emails (2020): Hackers exploited the pandemic by sending emails about “COVID-19 testing” or “stimulus checks” with malicious attachments.
These examples show how cyber phishing doesn’t just affect individuals—it can cripple global enterprises.
How to Prevent Phishing Attacks
Preventing phishing requires a combination of technology, training, and awareness.
Practical Tips to Avoid Phishing:
- Check the Sender – Verify email addresses, especially when they look slightly off.
- Hover Over Links – Don’t click blindly; preview URLs before opening them.
- Look for HTTPS – Ensure websites are secure before entering information.
- Enable Multi-Factor Authentication (MFA) – Even if credentials are stolen, MFA can stop attackers.
- Educate Employees – Regular training is key in businesses.
- Use Security Solutions – Spam filters, antivirus, and anti-phishing tools help reduce risks.
- Stay Updated – Keep software, browsers, and operating systems patched.
Remember: how phishing attack works is through deception, so prevention starts with skepticism.
Conclusion
Phishing is one of the most dangerous yet preventable cyber threats. The phishing definition shows us it’s about deception, while the meaning of phishing attacks reveals how criminals exploit human trust. By understanding the phishing definition in cyber security, learning the types of phishing scams, and knowing how phishing attack works, we can build stronger defenses against identity theft, data breaches, and financial fraud.
Businesses, banks, and individuals all face the same risk. The solution lies in awareness, proactive defense strategies, and choosing trusted cybersecurity partners.
At Trevonix, headquartered in London and serving clients globally, we specialize in helping organizations build resilience against phishing and other identity-related threats. With our expertise in Identity and Access Management (IAM), we ensure that your workforce, customers, and data stay secure.
Don’t let phishing compromise your future—partner with Trevonix to strengthen your cyber defense today.






