Digital transformation has changed how people work, shop, communicate, and access services. As organizations grow across multiple platforms, applications, and cloud environments, managing user identities has become more complex than ever. Users expect quick, safe access—without remembering multiple passwords or switching accounts repeatedly. This is where identity federation and the federated identity model offer a powerful solution.
Identity security today is no longer just about protecting systems. It is about ensuring seamless access, supporting hybrid environments, reducing friction, and enabling trusted interactions between users and applications. In this blog, you will learn what identity federation means, how the federated identity model works, why federated identity management matters, and how it helps modern organizations improve security and user experience.
Table of Contents
- What Is Federated Identity?
- Why Identity Federation Is Important Today
- How the Federated Identity Model Works
- Key Technologies Behind Identity Federation
- Federated Identity vs. Single Sign-On (SSO)
- Use Cases of Federated Identity
- Benefits of Identity Federation for Organizations
- Challenges and Best Practices
- Future of Federated Identity
- Conclusion: Why Trevonix Is the Trusted Partner for Identity and Access Management
What Is Federated Identity?
Identity federation is a system that allows users to access multiple applications, services, or domains using a single set of login credentials. In simple terms, it connects separate identity systems so that users do not need multiple accounts or passwords. Instead, one trusted identity provider is responsible for authenticating the user.
The federated identity model enables different organizations or departments to trust each other’s authentication processes. Instead of creating a new user account for every service, identity federation relies on secure token exchanges, trust relationships, and standardized protocols to verify identity.
This reduces friction, improves user experience, and strengthens security across distributed digital ecosystems. Modern enterprises use identity federation to support employees, customers, partners, and contractors across multiple platforms and clouds.
Why Identity Federation Is Important Today
Digital ecosystems have changed dramatically. Organizations now run on:
- Cloud applications
- SaaS platforms
- On-premise systems
- Mobile apps
- Partner services
- Multi-cloud networks
This complexity makes identity management difficult. Without the federated identity model, each system would require:
- Separate user accounts
- Repeated logins
- More password resets
- More identity risks
Organizations today need a safe, frictionless way to connect their systems. Identity federation provides this by ensuring trust between systems without sharing passwords directly.
The rise of remote work, hybrid environments, and cross-platform applications has made federated identity management essential for modern cybersecurity strategies.
How the Federated Identity Model Works
The federated identity model relies on trust relationships between three key components:
1. Identity Provider (IdP)
The IdP is responsible for verifying the user’s identity and issuing authentication tokens. Examples include:
- Azure AD
- Okta
- Google Identity
- Ping Identity
2. Service Provider (SP)
This is the application or service the user wants to access. The SP trusts the IdP to authenticate the user.
3. Trust Framework
The trust relationship ensures that the service provider accepts identity tokens from the identity provider.
Step-by-Step Workflow of Identity Federation
- A user tries to access a service provider’s application.
- The application redirects the user to the identity provider.
- The user logs in once to the identity provider.
- The IdP validates the user’s identity and generates a secure token.
- The token is shared with the service provider.
- The user gains access—without creating a new account.
This seamless trust flow is what makes the federated identity model highly efficient and secure.
Key Technologies Behind Identity Federation

To enable secure identity federation, several protocols and technologies are used:
1. SAML (Security Assertion Markup Language)
A widely used XML-based protocol for exchanging identity information across organizations. Common in enterprise applications.
2. OAuth 2.0
Used mainly for delegated access. Allows users to grant applications limited access to resources without sharing passwords.
3. OpenID Connect (OIDC)
A modern identity layer built on OAuth 2.0. Popular for consumer apps and mobile services.
4. JSON Web Tokens (JWT)
A compact, secure way of sharing claims and identity details across services.
5. API Gateways & Identity Brokers
They help route identity requests between different systems in the federated identity model.
Together, these technologies enable safe, scalable federated identity management across cloud and hybrid environments.
Federated Identity vs. Single Sign-On (SSO)
Many people confuse identity federation with single sign-on. While they are related, they are not the same.
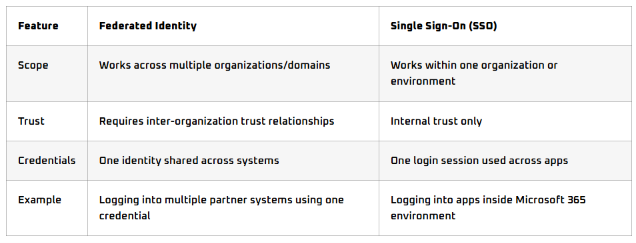
Identity federation is broader and more powerful than SSO. The federated identity model allows organizations to trust external authentication sources, enabling seamless collaboration between companies and partners.
Use Cases of Federated Identity
Identity federation is used across industries and business models. Some common examples include:
1. B2B Partner Access
Companies allow partners or vendors to access portals using their own corporate identities.
2. Customer Single Login Across Multiple Brands
Large corporations with multiple brands offer unified login experiences to enhance customer satisfaction.
3. Multi-Cloud Access
Enterprises use identity federation to connect AWS, Azure, and Google Cloud identities.
4. Education Sector
Students use one identity to access learning systems, library portals, and collaboration tools.
5. Government Services
Citizens authenticate once and access multiple services securely.
6. Healthcare
Doctors, insurers, and labs share identity authentication safely.
Identity federation supports all these scenarios without duplicating identities or storing multiple credentials.
Benefits of Identity Federation for Organizations

The federated identity model brings significant advantages across security, user experience, and operational efficiency. Below are the key benefits:
1. Improved User Experience
No more juggling multiple passwords. Users authenticate once and access everything they need.
Benefits:
- Fewer logins
- Less complexity
- Faster onboarding
- Better satisfaction
This is especially important in customer-facing applications.
2. Stronger Security
Identity federation reduces the attack surface because:
- Passwords are not stored or shared across multiple systems
- Phishing risks decrease
- Authentication happens at a trusted identity provider
This centralized control strengthens overall security.
3. Lower IT Workload
Federated identity management helps reduce:
- Password reset requests
- Duplicate accounts
- Manual provisioning
- Identity sprawl
IT teams can focus more on strategy rather than day-to-day identity issues.
4. Easier Compliance and Governance
With one trusted identity system controlling authentication, it becomes easier to maintain:
- Access logs
- Audit trails
- Policy enforcement
- Compliance with regulations such as GDPR, HIPAA, and ISO
Identity federation ensures consistent governance across environments.
5. Scalability Across Cloud and Hybrid Environments
Enterprises can expand easily because the federated identity model supports:
- Multi-cloud
- Hybrid apps
- Third-party integrations
- Cross-organization collaborations
As organizations grow, identity federation keeps access secure and simple.
Challenges and Best Practices
Although identity federation delivers major benefits, it also comes with challenges that organizations must manage.
Common Challenges
1. Building Trust Relationships
Organizations must establish legal, technical, and security trust agreements.
2. Protocol Complexity
SAML, OAuth, and OIDC require expert configuration.
3. Legacy Applications
Older systems may not support federation without modernization.
4. Misconfiguration Risks
Incorrect policies can expose sensitive data or create access gaps.
Best Practices for Success
1. Choose a Strong Identity Provider
A reliable IdP ensures smooth authentication and token management.
2. Use Modern Protocols
Prefer OIDC and OAuth for modern apps; use SAML for enterprise systems.
3. Implement Zero Trust Principles
Even with identity federation, continuous verification is necessary.
4. Regular Security Audits
Check token lifetimes, MFA adoption, and federation policies regularly.
5. Train Administrators and Users
Awareness reduces misuse and enhances trust relationships.
The Future of Federated Identity
As digital ecosystems expand, the federated identity model will continue to evolve. Several trends will shape its future:
1. Passwordless Authentication
Biometrics and FIDO-based solutions will reduce reliance on passwords.
2. Decentralized Identity (DID)
Users will control their own identities, supported by blockchain-based systems.
3. AI-Driven Identity Security
AI will detect anomalies and identity threats in real time.
4. Global Trust Networks
More industries will build shared identity networks to reduce friction.
5. Zero Trust Integration
Identity federation will become a core component of Zero Trust architecture.
As cybersecurity threats grow, federated identity management will remain essential for enabling secure, seamless digital experiences across complex environments.
Conclusion: Why Trevonix Is Your Trusted IAM Partner
Identity federation and the federated identity model are essential for modern, scalable, and secure digital systems. They simplify access, strengthen security, reduce IT workload, and support multi-cloud environments—all while providing fast and seamless user experiences. With strong federated identity management practices, organizations can confidently grow and innovate without compromising identity security.
To implement these capabilities effectively, organizations need a trusted partner with deep expertise.
This is where Trevonix stands out.
Trevonix is a global company headquartered in London, with primary markets in the US, UK, and Europe, and secondary markets across the Middle East, APAC, and ANZ. Trevonix is the trusted partner for businesses seeking secure, seamless, and scalable Identity and Access Management (IAM) solutions.
Our expert consultants deliver tailored cybersecurity strategies that help organizations:
- Protect digital identities
- Enhance user experiences
- Achieve compliance with evolving standards
- Implement strong identity federation architectures
- Build secure multi-cloud identity ecosystems
From advisory and architecture to implementation, integration, and managed services, Trevonix provides end-to-end IAM expertise. We support critical initiatives such as:
- Zero Trust
- Identity Threat Detection and Response
- IAM Cloud Transformation
- Privileged Access Management (PAM)
- Federated identity management deployment
Partnering with leading global cybersecurity vendors, we help organizations stay resilient against modern threats while delivering frictionless, secure access for employees, customers, and partners.
In a world where identity is the new security perimeter, Trevonix ensures your organization stays protected, compliant, and future-ready.






