In today’s rapidly evolving digital landscape, privileged access is one of the most targeted and exploited attack vectors in any organization. As companies move to the cloud and adopt Zero Trust models, the need for modern, scalable, and secure Privileged Access Management (PAM) solutions has grown exponentially. Enter Okta PAM—a cloud-native approach to securing critical systems, streamlining access, and strengthening enterprise identity posture.
Whether you're a cybersecurity professional, IT manager, or CISO, understanding Okta PAM is crucial to maintaining a strong security foundation in a multi-cloud, hybrid world. This guide offers a deep dive into the Okta Privileged Access Management offering—covering its features, benefits, use cases, pricing, and how it stands out from traditional PAM tools.
Table of Contents
- What Is Okta PAM?
- Key Features of the Okta PAM Module
- Benefits of Using the Okta PAM Solution
- Use Cases of Okta PAM
- Okta PAM Pricing: What to Expect
- How Okta PAM Compares to Traditional PAM Tools
- Conclusion
What Is Okta PAM?
Okta PAM, or Okta Privileged Access Management, is a modern cloud-native solution designed to manage and secure privileged access across hybrid and cloud environments. It enables organizations to control, monitor, and audit access to critical infrastructure without relying on legacy on-premise PAM tools.
Built on the Okta Identity platform, Okta PAM integrates seamlessly with other identity services like Okta Single Sign-On (SSO), Okta Adaptive MFA, and Lifecycle Management. It brings together identity and access controls in one unified, secure environment.
Cloud-Native Architecture
Unlike traditional PAM tools that require complex on-prem deployments, Okta PAM is born in the cloud. Its lightweight and scalable architecture supports modern DevOps workflows and provides immediate access without VPNs or jump servers.
Zero Trust Support
Okta PAM is designed around the principles of Zero Trust. It assumes no user or device is inherently trusted. It requires continuous verification, context-aware authentication, and least-privilege enforcement—all essential components of any modern cybersecurity strategy.
Security-First Approach
Okta places a strong emphasis on security by design. With features like just-in-time (JIT) access, ephemeral credentials, and full session auditing, Okta PAM ensures that your most sensitive environments are protected from misuse and threats—internal or external.
Key Features of the Okta PAM Module
The Okta PAM module includes several powerful features that make it a top choice for modern enterprises:
1. Just-in-Time Access (JIT)
With Okta PAM, access is granted only when needed and only for the minimum required duration. JIT access drastically reduces the attack surface by avoiding standing privileges.
2. Ephemeral Credentials
Instead of using shared or static passwords, Okta PAM module issues temporary, time-bound credentials that expire after use. This reduces the risk of credential theft and privilege misuse.
3. Session Recording and Auditing
All privileged sessions can be recorded and audited in real-time. This provides full visibility and traceability for compliance and forensic investigations.
4. Approval Workflows
Integrate fine-grained approval workflows before granting privileged access. This ensures that access is always intentional and authorized.
5. Secure Access to Infrastructure
Okta PAM solution supports direct browser-based access to critical infrastructure (like Linux/Windows servers, Kubernetes clusters, and databases) without needing a VPN or jump box.
6. Policy-Based Access Control
Admins can create and enforce dynamic policies that govern who can access what, under what conditions (user, location, time, risk, etc.).
7. Integration with DevOps Tools
Designed to integrate smoothly with CI/CD pipelines and tools like Terraform, Ansible, and GitHub Actions, the Okta PAM solution enhances security without disrupting developer workflows.
Benefits of Using the Okta PAM Solution
Adopting the Okta PAM solution brings several business and security benefits:
1. Reduce Risk of Data Breaches
By eliminating standing privileged credentials and enforcing JIT access, Okta privileged access management significantly reduces the chances of breaches due to compromised accounts.
2. Accelerate Zero Trust Initiatives
Okta PAM enables Zero Trust implementation by ensuring every access request is verified, least-privileged, and contextualized.
3. Simplify Compliance
Meet compliance mandates such as SOX, HIPAA, GDPR, PCI-DSS, and more by maintaining audit logs, access trails, and session recordings—all provided by the Okta PAM module.
4. Enable Secure Remote Work
As hybrid and remote work becomes the norm, Okta PAM provides seamless, secure, VPN-less access to critical systems from anywhere.
5. Streamline Operations
Centralized access management reduces IT overhead, simplifies user provisioning, and improves incident response times.
Use Cases of Okta PAM
Here are some real-world use cases where the Okta PAM solution delivers exceptional value:
1. Secure DevOps Environments
Engineering teams need on-demand access to infrastructure. With Okta PAM, they can get secure and auditable access without compromising productivity.
2. Protect Critical IT Assets
Privileged access to servers, databases, and cloud consoles is a common target for attackers. Okta privileged access ensures only authorized users get access—and only when truly needed.
3. Merge and Acquisition Scenarios
In M&A situations, new teams require access to shared infrastructure. Okta PAM enables secure, temporary, and controlled access without long-term risk.
4. Regulatory Audits and Investigations
When auditors require logs of privileged sessions, Okta PAM module provides complete, time-stamped, and tamper-proof records.
5. Insider Threat Prevention
Insiders with privileged access are a major risk. Okta privileged access management uses real-time monitoring and conditional policies to detect and prevent misuse.
Okta PAM Pricing: What to Expect
Okta PAM pricing follows a modular and flexible approach based on the organization's needs. While exact costs depend on usage, number of users, and deployment complexity, here are key pricing considerations:
1. Per-User Pricing
Most Okta PAM pricing models are subscription-based and charge per privileged user per month.
2. Tiered Feature Sets
Different pricing tiers unlock different features—such as advanced session recording, approval workflows, and third-party integrations.
3. Volume Discounts
Large enterprises may receive custom Okta PAM pricing packages based on usage and scale.
4. Add-On Costs
Additional costs may include integrations with SIEM tools, API access, and support plans.
To get accurate Okta PAM pricing, it’s recommended to contact an authorized Okta partner or reseller.
How Okta PAM Compares to Traditional PAM Tools
Legacy PAM tools often fall short in today’s cloud-first environments. Here's how Okta PAM stacks up:
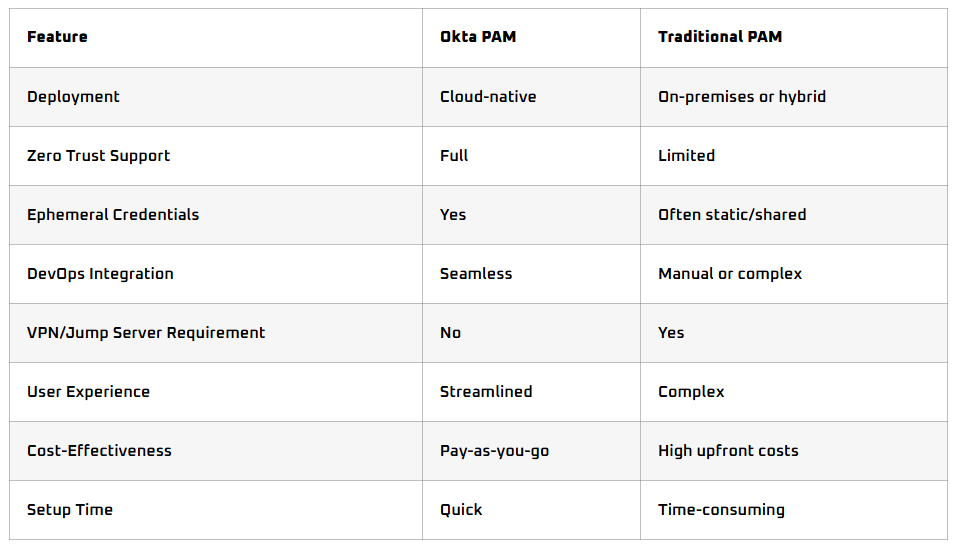
Okta privileged access management brings the agility, scalability, and security needed in today’s digital transformation journey—something that older tools simply cannot match.
Conclusion
Privileged access is a high-value target for attackers, and traditional PAM solutions are no longer sufficient. Okta PAM offers a modern, secure, and scalable approach to managing privileged access in today’s cloud-native world. With just-in-time access, ephemeral credentials, and Zero Trust alignment, Okta privileged access management empowers organizations to protect their most sensitive assets without slowing down operations.
Whether you're securing DevOps pipelines, enabling remote administration, or preparing for audits, the Okta PAM module delivers unmatched value with minimal complexity.
Organizations looking for a partner to implement, support, and optimize their Okta PAM solution can turn to trusted experts like Trevonix. Trevonix specializes in identity and access management services, including Okta PAM, and helps businesses navigate complex security challenges with precision and agility.






