In today’s digital-first world, organizations operate across cloud applications, remote work environments, SaaS platforms, and hybrid identity systems. This rapid expansion has made identity the new security perimeter. Every employee, vendor, system, application, and even bot has an identity—and each identity holds access that can either strengthen or compromise an organization’s security posture.
This is where Identity Governance and Administration (IGA) becomes essential.
As cybersecurity threats increase and compliance standards become more complex, enterprises need a structured, scalable, and automated way to govern digital identities, monitor privileges, and ensure that the right people have the right access at the right time. Identity governance and administration provides that foundation.
This guide offers a comprehensive, deeply detailed, and practical understanding of identity governance and administration - how it works, why businesses need it, core components, benefits, implementation steps, challenges, best practices, and how modern solutions revolutionize digital identity security.
Table of Contents
- What Is Identity Governance and Administration (IGA)?
- Difference Between Identity Governance and Identity Administration
- Why IGA Is Critical in Today’s Digital World
- Core Components of Identity Governance and Administration
- How IGA Works: Step-by-Step
- Key Capabilities of a Modern IGA Solution
- Common Challenges Without IGA
- Benefits of Implementing Identity Governance and Administration
- IGA Use Cases Across Industries
- Cloud IGA vs Traditional On-Prem IGA
- Best Practices for Successful IGA Implementation
- Future Trends in Identity Governance
- Conclusion
What Is Identity Governance and Administration (IGA)?
Identity Governance and Administration (IGA) is a framework of policies, processes, and technologies that manage and secure user identities within an organization. It ensures that every digital identity—employees, customers, contractors, partners, bots, and service accounts—has appropriate access to systems, data, and applications.
IGA combines two major functions:
- Identity Governance (ensures compliance, visibility, and oversight of identities and access)
- Identity Administration (provisioning, deprovisioning, lifecycle management, and access control)
In simple words:
Identity governance and administration helps organizations monitor identity access, enforce security policies, meet compliance rules, and automate identity lifecycle processes.
Through strong identity governance, businesses gain visibility into who has access, why they have access, and whether they should continue to have that access.
Difference Between Identity Governance and Identity Administration

Although often used together, the terms represent two distinct functions.
Identity Governance
Identity governance focuses on oversight, auditing, and compliance. It answers questions such as:
- Are user access rights appropriate?
- Do access privileges violate any compliance rules?
- Is access being reviewed periodically?
- Are there toxic combinations of permissions?
Governance ensures continuous monitoring and provides full visibility across all identities.
Identity Administration
Identity administration focuses on operational identity lifecycle management, including:
- Creating new accounts
- Modifying access as roles change
- Removing access when employees leave
- Automating provisioning across multiple systems
Administration is action-oriented, while governance is visibility- and compliance-oriented.
The Power of Their Combination: IGA
Together, identity governance and administration create a unified, efficient, and secure identity ecosystem.
Why IGA Is Critical in Today’s Digital World
Organizations are facing challenges such as:
- Distributed workforce and global hiring
- Dependence on cloud SaaS applications
- Insider threats and account misuse
- Increasing compliance demands (GDPR, HIPAA, SOX, ISO 27001)
- Privilege creep and orphan accounts
- Multi-cloud identity sprawl
Without identity governance and administration, enterprises struggle to maintain visibility and control.
Key Reasons IGA Is Essential
- Accounts and access explode across cloud ecosystems.
- Cyber threats target identity systems first.
- Regulations demand strict auditing and governance.
- Manual identity management creates risks and inconsistencies.
- Zero Trust security requires strong identity governance.
A modern security program cannot exist without IGA.
Core Components of Identity Governance and Administration
To understand IGA, it’s important to explore its main components. These define how identity governance, identity administration, and orchestration work together.
1. Identity Lifecycle Management
The ability to automate the creation, updating, and removal of identities across systems.
Includes:
- User onboarding
- Role changes
- Offboarding
- Contractor/partner identity management
2. Access Request Management
A platform where users request access to applications or systems.
Features:
- Self-service access portal
- Automated routing
- Manager or role-based approval
- Policy-based access assignment
3. Access Certification (Access Reviews)
(One of the strongest pillars of identity governance)
Ensures periodic access reviews to prevent over-permissioning.
Helps meet compliance frameworks like SOX, PCI DSS, and ISO 27001.
4. Role-Based Access Control (RBAC)
Defines roles and assigns access based on job responsibilities.
RBAC reduces privilege creep and simplifies administration.
5. Segregation of Duties (SoD)
Prevents users from having conflicting permissions that could lead to fraud or misuse.
Example:
A user approving payments should not also create vendors.
6. Policy Management
Enforces identity governance through policies such as:
- Password complexity
- Access expiry rules
- Privilege escalation prevention
7. Analytics and Reporting
Provides:
- Risk scoring
- Audit trails
- Identity activity logs
- Compliance reports
This component is essential for identity governance.
How IGA Works: Step-by-Step
The identity governance and administration lifecycle consists of several steps:
Step 1: Identity Creation
A new employee or contractor is added to HR systems, triggering automatic identity generation.
Step 2: Access Provisioning
Based on roles, the user is automatically granted access to apps like:
- ERP systems
- CRM
- Collaboration tools
Step 3: Access Monitoring
Identity governance tools track:
- Privilege changes
- Dormant accounts
- Access anomalies
- SoD violations
Step 4: Access Certification
Managers periodically review user access and confirm or revoke permissions.
Step 5: Access Modification
As employees change roles, IGA updates access rights automatically.
Step 6: Offboarding
IGA ensures immediate disablement of user accounts and removal of all privileges.
Step 7: Continuous Governance
Identity governance ensures ongoing monitoring, risk scoring, and compliance.
Key Capabilities of a Modern IGA Solution
A modern IGA platform is more than a provisioning tool—it is an intelligent, automated identity governance system.
1. Automated Provisioning and Deprovisioning
Removes manual IT workload and eliminates human error.
2. AI/ML-Based Access Recommendations
Suggests least-privilege access.
3. Unified Identity Repository
Creates a single source of truth for all digital identities.
4. Cloud-Ready Architecture
Supports multi-cloud, SaaS applications, and hybrid environments.
5. Identity Governance Analytics
Provides insights into:
- High-risk accounts
- Access anomalies
- Privilege misuse
6. API Integrations with Enterprise Apps
Seamless integration with Microsoft 365, AWS, Salesforce, HRMS systems, and legacy apps.
Common Challenges Without IGA
Organizations lacking identity governance and administration face risks such as:
- Excessive permissions
- Orphan accounts
- Insider threats
- Difficulty preparing for audits
- Manual provisioning errors
- Privilege creep
- Incomplete offboarding
- Lack of visibility into identity risks
Such security gaps often lead to data breaches, financial loss, and compliance violations.
Benefits of Implementing Identity Governance and Administration

Implementing IGA transforms security and efficiency across an organization.
1. Stronger Security
Reduces unauthorized access and identity attacks.
2. Compliance Assurance
Simplifies audits and meets regulatory requirements.
3. Operational Efficiency
Automates labor-intensive identity tasks.
4. Reduced IT Workload
Self-service tools reduce dependency on IT teams.
5. Minimized Risk of Human Error
Automated workflows prevent gaps caused by manual processes.
6. Better Visibility
Identity governance provides complete visibility into access relationships.
7. Zero Trust Enablement
Identity is continuously validated, aligning with Zero Trust principles.
IGA Use Cases Across Industries
1. Banking & Finance
Preventing fraud, managing SoD conflicts, ensuring compliance with SOX and PCI DSS.
2. Healthcare
Protecting patient data and meeting HIPAA compliance.
3. Retail & E-commerce
Securing customer data and supporting large, seasonal workforce identity shifts.
4. Manufacturing
Managing contractors, third-party vendors, and IoT identities.
5. Government
Strict identity governance policies to protect confidential information.
6. AEC, IT, and SaaS Companies
Managing multi-cloud environments and securing identities across distributed teams.
Cloud IGA vs Traditional On-Prem IGA
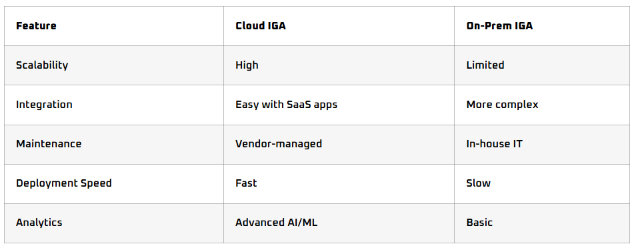
Modern enterprises increasingly prefer cloud-first identity governance and administration due to flexibility and advanced capabilities.
Best Practices for Successful IGA Implementation
- Start with a clear identity governance policy.
- Integrate IGA with HR systems for accurate identity lifecycle management.
- Automate provisioning and deprovisioning using workflows.
- Use role-based and attribute-based access controls.
- Conduct regular access reviews.
- Monitor privileged accounts closely.
- Ensure segregation of duties (SoD) controls.
- Adopt risk-based access certification.
- Enable self-service access features.
- Continuously update governance rules.
Future Trends in Identity Governance
The identity landscape is rapidly evolving. Future IGA systems will include:
- AI-driven identity governance
- Behavioral identity analytics
- Automated risk-based provisioning
- Cross-app identity orchestration
- Identity threat detection
- Predictive access governance
The next era of identity governance and administration will be intelligent, automated, and cloud-native.
Conclusion: Why Trevonix Is the Future of IGA
As organizations scale, securing identity becomes the backbone of enterprise security. Implementing identity governance and administration is no longer optional—it is critical for protecting systems, ensuring compliance, and maintaining operational efficiency.
This is where Trevonix stands out as a global leader.
Trevonix, a global identity security and access management company headquartered in London, offers advanced, modern, cloud-ready solutions that simplify and automate identity governance. With strong capabilities in access controls, lifecycle automation, compliance governance, identity monitoring, and enterprise integrations, Trevonix empowers organizations across the US, UK, Europe, the Middle East, APAC, and ANZ.
Trevonix helps enterprises build a secure, compliant, and efficient digital identity foundation—making it the ideal partner in your IGA journey.






