As organizations continue their rapid shift to cloud computing, Software-as-a-Service (SaaS), and remote work models, traditional security approaches are no longer enough. The old idea of protecting a network perimeter has faded. Today, users access applications from anywhere, on any device, and often without ever touching a corporate network.
This shift has placed digital identity at the center of cybersecurity strategy. Who is accessing what, from where, and under what conditions now matters more than where the application is hosted. This is where IDaaS (Identity as a Service) plays a critical role.
IDaaS provides a modern, cloud-native approach to managing identities, authentication, and access across distributed IT environments. It enables organizations to secure users, applications, and data while improving agility and user experience.
In this comprehensive guide, we will explain what IDaaS is, how identity as a service works, why cloud IDaaS has become essential for modern security, and how organizations can successfully adopt it as part of a broader Identity and Access Management (IAM) strategy.
Table of Contents
- What Is IDaaS (Identity as a Service)?
- Core Components of an IDaaS Platform
- Why Cloud IDaaS Is Becoming Essential
- Key Benefits of Identity as a Service
- IDaaS vs Traditional IAM Solutions
- Role of IDaaS in a Modern IAM Strategy
- Common Use Cases for Cloud IDaaS
- Security and Compliance with IDaaS
- Challenges and Considerations When Adopting IDaaS
- How to Choose the Right IDaaS Provider
- How Trevonix Helps Organizations Implement Cloud IDaaS
- Conclusion
What Is IDaaS (Identity as a Service)?
Simple definition of IDaaS
IDaaS stands for Identity as a Service. It is a cloud-based identity management solution that provides authentication, authorization, and access control services over the internet.
Instead of hosting identity systems on internal servers, organizations use identity as a service to manage users and access through a secure cloud platform. This approach reduces complexity, improves scalability, and supports modern digital environments.
How identity as a service works in the cloud
In a cloud IDaaS model, identity services are delivered through a centrally managed platform hosted by a service provider. Users authenticate once, and the platform verifies their identity using security policies such as passwords, multi-factor authentication, or adaptive access controls.
Once authenticated, users can securely access approved applications without repeated logins. The IDaaS platform continuously evaluates access based on context, behavior, and risk.
Key difference between on-prem IAM and cloud IDaaS
Traditional on-prem IAM systems require hardware, maintenance, upgrades, and internal expertise. Scaling them is time-consuming and expensive.
By contrast, IDaaS is:
- Cloud-native
- Subscription-based
- Rapidly scalable
- Easier to integrate with SaaS and cloud applications
Cloud IDaaS solutions update automatically and adapt quickly to new threats and technologies.
Why organizations are moving identity to the cloud
Organizations are moving to identity as a service because:
- Applications are increasingly cloud-based
- Workforces are remote and hybrid
- Cyber threats target credentials, not networks
- Businesses need faster onboarding and offboarding
- IT teams need flexibility and lower operational overhead
Core Components of an IDaaS Platform
A modern IDaaS platform includes several essential components that work together to secure identities and access.
User authentication and authorization
Authentication verifies who the user is. Authorization determines what the user can access. IDaaS platforms enforce both consistently across applications.
Single Sign-On (SSO)
SSO allows users to log in once and access multiple applications securely. This improves productivity while reducing password fatigue and security risks.
Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring additional verification, such as OTPs, biometrics, or hardware tokens. MFA is a standard feature of cloud IDaaS solutions.
Identity lifecycle management
Identity as a service automates user provisioning, role changes, and deprovisioning across systems. This reduces human error and prevents orphaned accounts.
Directory services and federation
IDaaS platforms often replace or extend traditional directories and support identity federation across organizations, partners, and cloud services.
API and application integrations
Modern IDaaS solutions integrate easily with SaaS apps, cloud platforms, and custom applications through APIs and standard protocols.
Why Cloud IDaaS Is Becoming Essential

Cloud-first and SaaS-driven environments
Most organizations now rely on dozens or even hundreds of SaaS applications. Managing access manually is no longer practical. Cloud IDaaS provides centralized control across all environments.
Hybrid and remote workforce needs
Employees, contractors, and partners access systems from various locations and devices. IDaaS ensures secure, consistent access without relying on corporate networks.
Increasing identity-based cyber attacks
Phishing, credential theft, and account takeover attacks are rising. Attackers target identities because they are the easiest entry point. IDaaS strengthens authentication and monitoring.
Regulatory and compliance pressure
Regulations demand stronger access controls, visibility, and audit trails. Identity as a service simplifies compliance through centralized policy enforcement.
Identity becoming the new security perimeter
With no clear network boundary, identity is now the primary control point. IDaaS enforces security based on who the user is, not where they connect from.
Key Benefits of Identity as a Service
Centralized Identity Management
IDaaS provides one platform to manage users, applications, and access rights. This reduces identity sprawl and administrative complexity.
Improved Security Posture
Strong authentication, MFA, and continuous monitoring reduce the risk of breaches. Identity as a service minimizes password-related vulnerabilities.
Scalability and Flexibility
Cloud IDaaS scales easily as organizations grow. New users, apps, and locations can be added without infrastructure changes.
Better User Experience
SSO and streamlined access improve productivity. Faster onboarding and offboarding enhance employee and partner experiences.
Cost Efficiency
IDaaS eliminates the need for on-prem infrastructure and reduces maintenance costs. Predictable subscription pricing simplifies budgeting.
IDaaS vs Traditional IAM Solutions
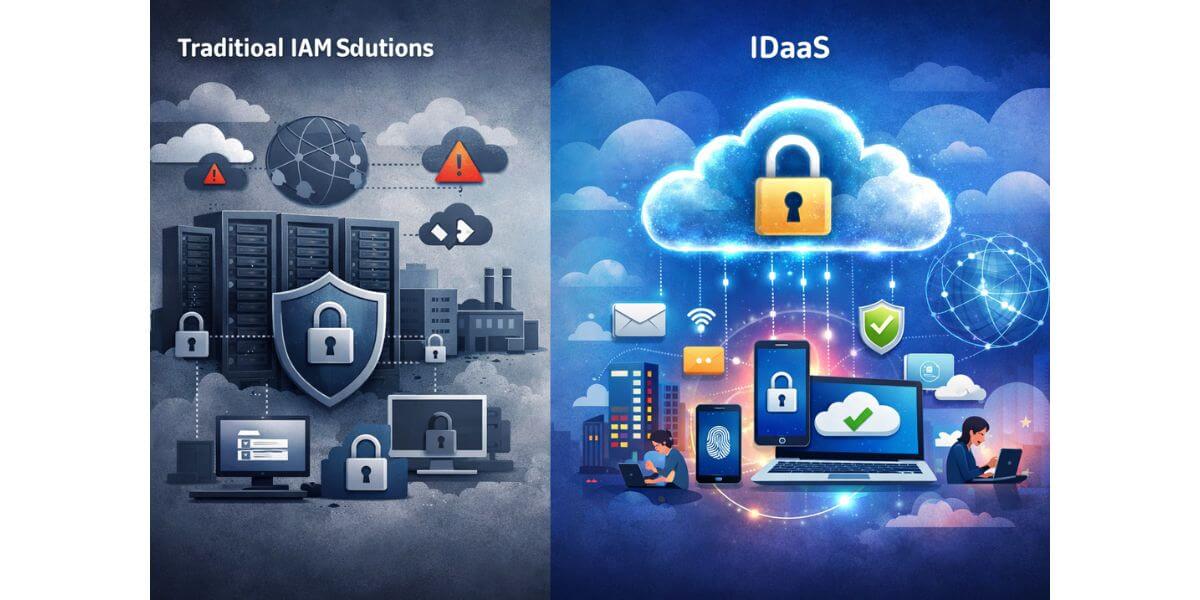
Traditional IAM systems were designed for static, on-prem environments. They struggle with cloud integration, scalability, and remote access.
IDaaS offers:
- Faster deployment
- Cloud-native security
- Better SaaS compatibility
- Lower operational burden
For modern organizations, cloud IDaaS is no longer optional—it is foundational.
Role of IDaaS in a Modern IAM Strategy
IDaaS is a core building block of modern IAM strategies.
Integration with Zero Trust security models
Zero Trust assumes no user or device is trusted by default. IDaaS enforces continuous verification and least privilege access.
Supporting least privilege and access governance
Identity as a service enables fine-grained access controls, role-based access, and governance workflows.
Enabling secure digital transformation
Cloud IDaaS supports cloud migration, DevOps, and digital innovation without compromising security.
Common Use Cases for Cloud IDaaS
- SaaS application access management
- Remote and hybrid workforce authentication
- Partner and customer identity management
- Mergers and acquisitions
- Cloud migration initiatives
In each case, IDaaS simplifies access while improving security and visibility.
Security and Compliance with IDaaS
Meeting regulatory standards
Cloud IDaaS helps meet GDPR, ISO 27001, SOC 2, and other standards through centralized controls.
Audit readiness and visibility
Detailed logs, reports, and dashboards improve audit readiness and accountability.
Policy enforcement and reporting
Security policies are applied consistently across all applications and users.
Data protection and identity governance
Identity as a service supports governance processes that protect sensitive data and reduce risk.
Challenges and Considerations When Adopting IDaaS
Application compatibility
Legacy applications may require integration planning.
Data residency and compliance
Organizations must consider where identity data is stored and processed.
Vendor lock-in risks
Choosing standards-based IDaaS platforms reduces dependency risks.
Importance of proper identity design
Poor identity architecture can create security gaps. Strategy matters as much as technology.
How to Choose the Right IDaaS Provider
When selecting an IDaaS provider, consider:
- Strong security features and certifications
- Support for SAML, OAuth, and OpenID Connect
- Proven scalability and performance
- Broad integration ecosystem
- Reliable support and managed services
A trusted provider ensures long-term success.
How Trevonix Helps Organizations Implement Cloud IDaaS
Trevonix helps organizations design, implement, and optimize cloud IDaaS solutions aligned with business and security goals. From identity strategy and architecture to deployment and governance, Trevonix ensures seamless integration with existing systems and future-ready IAM frameworks.
Conclusion
As cloud adoption accelerates and cyber threats continue to target identities, IDaaS has become a critical pillar of modern cybersecurity. Identity as a service enables organizations to secure access, improve user experience, and support scalable digital growth.
With identity now acting as the new security perimeter, cloud IDaaS provides the visibility, control, and resilience required in today’s distributed environments.
Trevonix, a global identity and cybersecurity services company headquartered in London, helps enterprises worldwide implement secure, scalable, and compliant IDaaS solutions. By combining deep IAM expertise with modern cloud technologies, Trevonix empowers organizations to protect identities and confidently embrace digital transformation.






