Yes. A user can be authenticated (verified) without being authorized to perform any specific actions.
In today's digital age, safeguarding user identities and ensuring that only authorized users access sensitive data is crucial for all organizations. Two fundamental concepts that play a critical role in this process are authentication and authorization. While these terms are often used interchangeably, they serve very different purposes within identity and access management (IAM). Understanding the key differences between authentication and authorization is essential for implementing secure systems and managing user access effectively.
This blog dives deep into the core differences, definitions, and real-world applications of authentication vs authorization. We will also cover frequently asked questions and discuss how companies like Trevonix help enterprises streamline IAM solutions.
Table of Contents
- What Is Authentication?
- What Is Authorization?
- Authentication vs Authorization
- Key Differences Between Authentication and Authorization
- Authentication vs Authorization FAQs
- Conclusion: How Trevonix Can Help
What Is Authentication?
Authentication is the process of verifying the identity of a user or system. When you log into a website, swipe your ID card, or use your fingerprint to unlock your phone, you're going through an authentication process. The goal is to ensure that the person or system trying to gain access is who they claim to be.
What is authentication in technical terms? It's the validation of credentials—such as usernames, passwords, biometrics, or tokens—against a system’s stored records.
Common Authentication Methods:
- Password-based authentication
- Two-factor authentication (2FA)
- Multi-factor authentication (MFA)
- Biometric authentication (fingerprints, facial recognition)
- Token-based authentication (like OTPs)
- Certificate-based authentication
Authentication is the first step in securing systems. Without it, there would be no way to verify the user’s identity.
What Is Authorization?
Once a user’s identity is verified through authentication, the next step is authorization. Authorization is the process of determining what a verified user is allowed to do. This includes access to resources, data, files, or systems.
What is authorization? It refers to the permissions granted to a user based on their role, level, or credentials after authentication is successfully completed.
Common Authorization Types:
- Role-based access control (RBAC)
- Attribute-based access control (ABAC)
- Policy-based access control
- Access Control Lists (ACLs)
For example, an employee may be authenticated to log into a company’s intranet, but only authorized to view HR documents, not financial records.
Authentication vs Authorization
To truly understand the differences between authentication and authorization, we need to explore how they function together in real-world scenarios.
Here’s a simple example:
- You enter your username and password to log into an application. The system checks your credentials—this is authentication.
- Once verified, the system determines that you are a ‘Manager’ and gives you access to managerial data but not admin features. This is authorization.
Both processes are part of a secure access management strategy, but they operate independently.
Authentication vs Authorization can be summarized as:
- Authentication: Who are you?
- Authorization: What are you allowed to do?
Key Differences between Authentication and Authorization
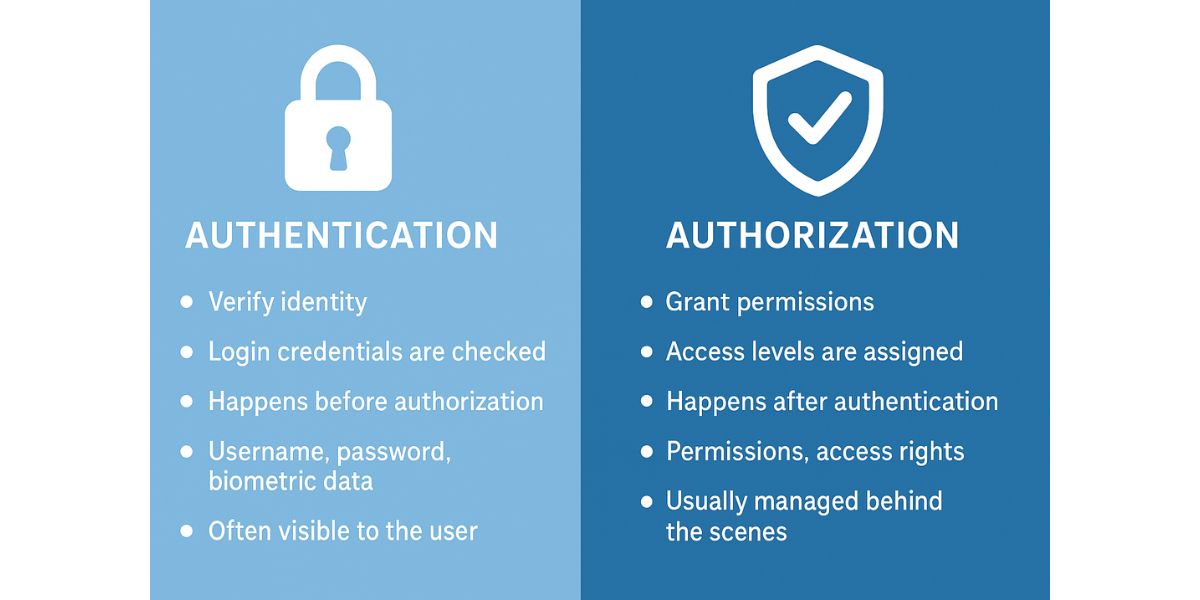
Let’s break down the key differences between authentication and authorization across multiple dimensions:
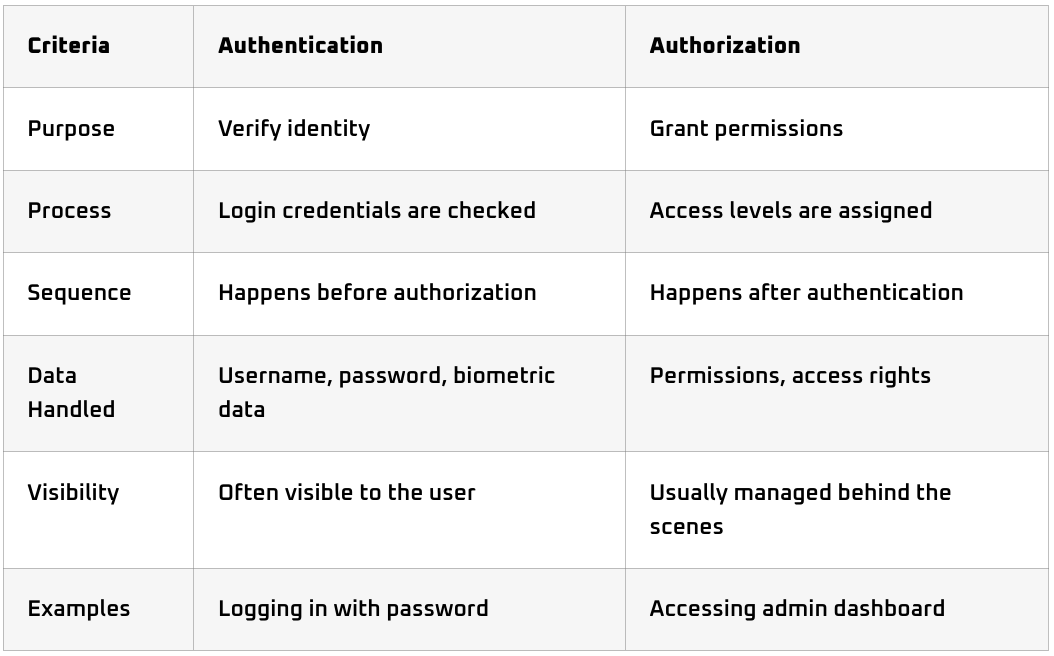
Real-World Examples:
- Authentication: Entering a password to access your email.
- Authorization: Being allowed to send emails but not change account settings.
These differences between authentication and authorization emphasize the importance of implementing both steps in your cybersecurity strategy.
Conclusion: How Trevonix Can Help
Understanding the authentication vs authorization paradigm is vital for any enterprise looking to enhance cybersecurity. Both elements are foundational to modern identity and access management systems.
Implementing robust authentication and authorization mechanisms helps prevent data breaches, ensures compliance, and protects sensitive business assets.
Trevonix, a leader in IAM solutions, offers end-to-end identity governance and access management services tailored to your organization’s needs. Whether you’re building a zero-trust architecture or optimizing existing IAM frameworks, Trevonix helps secure your digital environment efficiently and effectively.
By leveraging Trevonix’s IAM expertise, you can streamline access management, reduce identity-related risks, and enable secure digital transformation.






